Lacework named Leader (again): Perspectives on the G2 Spring Reports
G2, the largest and most trusted software marketplace, recently released its Spring 2023 Reports on cloud security vendors. Nearly 150,000 products and services are listed on G2, and more than 80 million people annually visit the site to make smarter software decisions. G2 vendor ratings are crowdsourced, based on reviews from the vendors’ own customers.
This blog breaks down the latest batch of G2 reports, hits some key highlights, and explains how Lacework landed in the Leader quadrant multiple times once again.
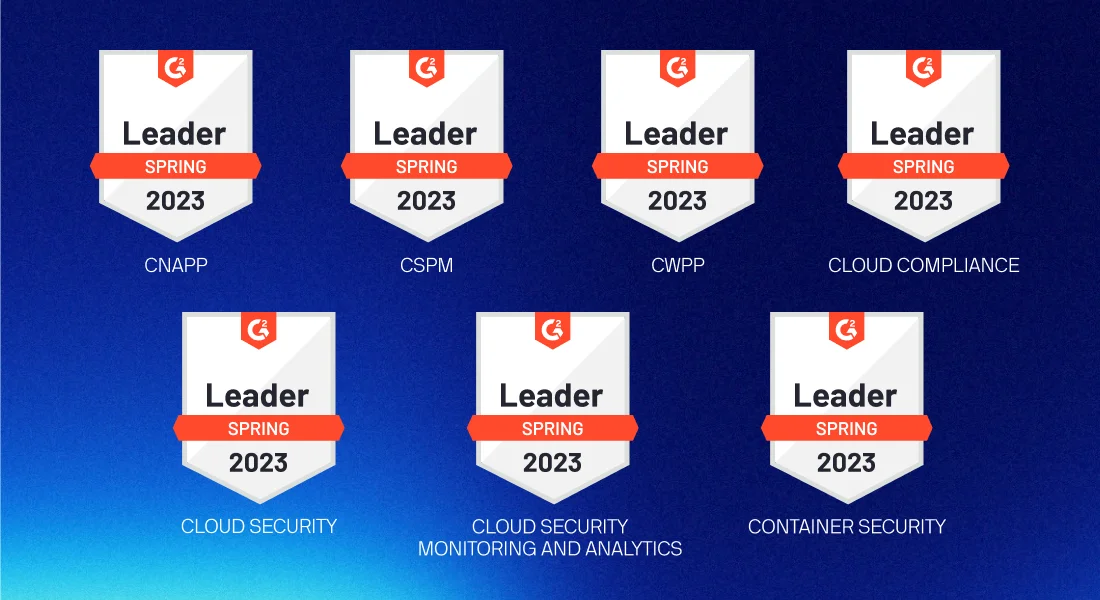
Lacework named Leader across 7 cloud security categories by satisfied customers
With the release of the G2 Spring Reports, Lacework was named Leader across 7 different cloud security categories, including:
- Cloud-Native Application Protection Platform (CNAPP)
- Cloud Security Posture Management (CSPM)
- Cloud Workload Protection Platform (CWPP)
- Cloud Compliance
- Cloud Security
- Cloud Security Monitoring and Analytics
- Container Security
This marks our first appearance in the CNAPP category, as this was the category’s inaugural appearance in G2 reports. It was also the first time Lacework was featured in the CSPM category — further proof that our innovative posture management investments have made a splash with customers and have cemented Lacework as a leading brand for CSPM. In fact, in a recent survey, nearly 70 percent of Lacework customers indicated that our posture management capabilities led them to choose our platform.
Speaking of our customers, we need to share this right off the top. We honestly can’t say enough about our customers. We stand convinced that we have the most collaborative, innovative, and smart customers in the entire industry. And while G2 has chosen to highlight Lacework as a Leader in the cloud security space, our platform evolution over the years has, in many ways, been driven by our customers’ challenges, pains, ideas, and successes. We appreciate being in the spotlight here, but we were driven into the spotlight by those who trust our platform to secure their businesses. And, for that, we are most grateful.
Alright, enough of the sappy stuff. Let’s highlight some of these G2 categories one-by-one.
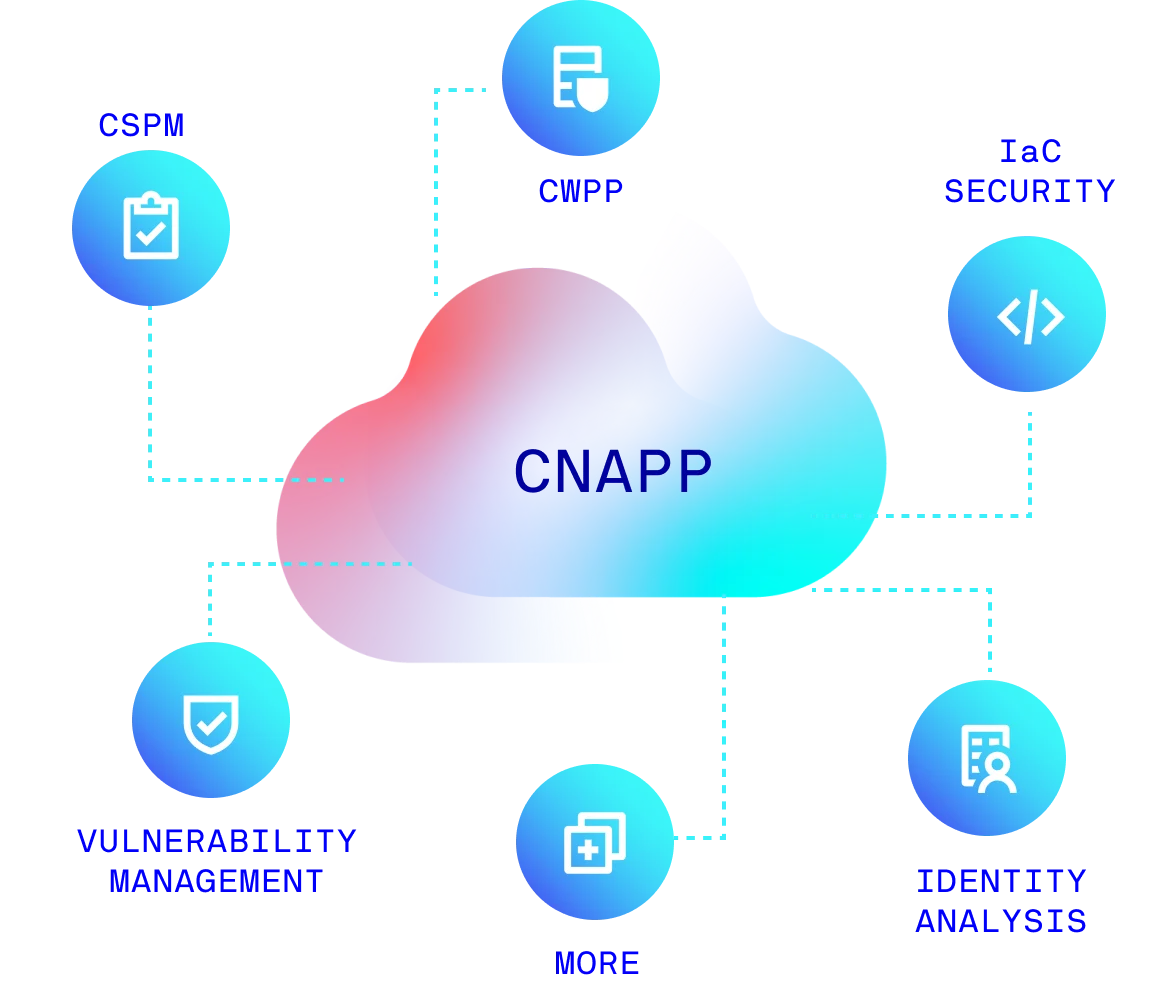
The only Leader offering a true CNAPP
Since the term’s inception in 2021, cloud-native application protection platforms (CNAPPs) have taken the cloud security world by storm. At its core, a CNAPP solves cloud security inefficiencies by consolidating build time and runtime cloud security tools into a single platform.
For years, the market was driven by point solutions that each could solve for one piece of the puzzle — vulnerability management, posture management, workload protection, infrastructure as code (IaC) security. But, in the cloud, these use cases don’t exist in isolation. What happens in build time affects runtime, and vice versa. Vulnerability severity depends on what’s actually in production. The most effective cloud security solutions reflect the nature of the cloud itself — integrated and seamless. Enter CNAPP.
A CNAPP is a single solution that offers build through runtime cloud protection via a variety of means, both agent-based and agentless.
A recent CNAPP vendor guide by the analyst that actually coined the term doubles-down on its original definition — that a CNAPP is a single solution that offers build through runtime cloud protection via a variety of means, both agent-based and agentless. According to their research, 60 percent of enterprises will invest in this type of single platform by 2025. And, of the 5 vendors featured as Leader in G2’s inaugural CNAPP grid, Lacework is proud to say that we’re the only vendor featured that follows the original CNAPP definition to a tee.
Some companies are good at detecting runtime threats. Some companies are great at providing snapshots of your security posture. But, unfortunately, without a combined approach that looks at all risk factors in the context of runtime or production data, your security team will waste time and money remediating risks that were not even exploitable and will always feel like it’s catching up from behind.
Instead of looking through multiple tools for the information we need, we have it all in one platform… By adopting a single platform, we fully eliminated five tools, which has saved us valuable time and reduced our costs.
Lacework: Leader in CSPM, automatically connects posture to running workloads
Cloud security posture management (CSPM) is critical for modern cloud security. CSPM tools monitor cloud applications, services, containers, and infrastructure to detect and remediate security risks like misconfigurations and vulnerabilities. But CSPM tools are most effective when they’re enhanced with the context that comes along with a broader cloud security platform.
Most CSPM tools are likely to surface and rank your cloud misconfigurations and vulnerabilities based on rules, signatures, and third-party risk feeds. But you’re still likely to be inundated with alerts, all trying to fight for your team’s attention. Only when you consider your risks in the context of your broader cloud environment are you able to truly identify and fix the greatest issues, unique to your own organization.
As a true code-to-cloud CNAPP, Lacework does that work for you. Our platform ingests your data across build time and runtime then connects the dots to find and surface the greatest issues with your own unique cloud posture. For example, in Fall 2022, Lacework released the Exposure Polygraph feature, which can build attack paths to tie internet-exposed vulnerabilities to databases in production. Security teams can, then, prioritize risks based on what cloud properties are actually impacted by the vulnerability or misconfiguration.
Before using Lacework, we spent an entire quarter focusing on risk assessment. Now, we can get the results instantly and remediate them in just a few weeks. Lacework has saved the security team a whole quarter of work.
Threat detection remains our core differentiator
A cloud workload protection platform (CWPP) is a security solution designed to safeguard applications and data stored in the cloud. The best workload protection is only possible with agent-based, continuous runtime monitoring. From the beginning, Lacework has held to this position and, consequently, has spent nearly a decade refining one of the most lightweight and stable runtime agents in history. And, now, because of that hard work, Lacework offers full agent and agentless build-to-runtime cloud security in a true, unified CNAPP platform.
Our agent, however, is only half of the story. Most CWPPs rely on traditional rules and signatures to detect threats. These legacy means don’t scale in the cloud, as alert queues fill with false positives and hide the real issues. Lacework offers behavior-based threat detection. Our platform automatically ingests your data and builds a baseline for your normal behavior, then surfaces any concerning deviations. This unique approach effectively makes rules optional, freeing up precious time and brainpower for your security team.
I would argue (that all the other tools we had) failed because Lacework Polygraph, within minutes of an attack beginning, was able to detect something that the others could not see. It outperformed everything we’ve been doing. I’m a huge fan.
Lacework: Leader in Cloud Compliance, puts audits on autopilot
Cloud compliance software is used to ensure regulatory standards and provide compliance controls for networks and cloud infrastructure. Compliance, while necessary, is often a distraction for bandwidth-deprived security teams. Without the proper tools, fulfilling audit requests can be an exercise in the manual and mundane, and can distract security teams from the high-value work of eliminating critical vulnerabilities and finding real cloud threats.
Lacework is honored to, once again, be named Leader in compliance category. Lacework offers automated compliance maintenance and reporting that is, again, a part of a single dashboard spanning your entire cloud environment. However, to us, compliance is just one piece of the larger puzzle. To be truly compliant, you need to look for a solution that not only can identify risks against a compliance framework but can quickly identify areas where compliance has failed.
With Lacework, we have the assurance that an organization’s security posture is continuously being looked at. To do the same thing with other technologies, it takes at least five different tools, which gets expensive and arduous to manage.
Customers choose Lacework for cloud security innovation
In addition to the categories above, Lacework was named Leader for Cloud Security (in general), Cloud Security Monitoring and Analytics, and Container Security.
Lacework is honored to find itself in the Leader position once again across multiple cloud security categories. Since our founding in 2017, we’ve held fast to two things: an unwavering commitment to our customers and a firm belief that cloud security is a data problem. For us, each new release of these G2 reports is affirmation of those ideals.
From the beginning, we’ve designed our unified platform to ingest and comprehend as much cloud data as possible to provide the best security possible — by both agent-based or agentless means. These G2 reports, other recent writings by leading analysts, and recent strategic vendor partnerships seem to indicate that our foundational principle was right and will stand the test of time and that other cloud security fads simply aren’t enough to protect against modern risks and threats.
Interested in learning more about the Lacework CNAPP and why our G2 customers gave us a 9.7/10 on Product Direction? Contact us to learn more or check out our library of on-demand product demos.
Suggested for you