Kubernetes security and visibility
Harden Kubernetes security posture (KSPM), find vulnerabilities, detect unusual behavior, and spot runtime threats.

Highly dynamic and configurable K8s cause security issues
Security risks have become more prominent, as development teams accelerate their use of Kubernetes to achieve speed and efficiency goals.

Complex environments obstruct visibility
The dynamic nature of K8s creates complexity and blind spots for security and compliance. Secure K8s with comprehensive visibility.
Rules alone cannot protect against threats
Rules only find known risks, and can break in K8s environments. Automate security to detect unknown threats without writing complex rules.
Alerts without context are just noise
Hundreds or thousands of alerts overwhelm security. Force multiply your teams with Composite Alerts to accelerate response time and provide meaningful insight with security context.
whitepaper
The Role of Kubernetes in Cloud Security
Read the whitepaper to learn how to apply effective security so your organization has visibility, threat detection, and anomaly analysis to risks and threats for Kubernetes-deployed infrastructures, including publicly exposed and unsecured API servers and management consoles.
Read White Paper
BENEFITS
Run Kubernetes with confidence
Accelerate Kubernetes and container usage with security and compliance control from build to runtime, across K8s control and data planes.
Secure from the beginning
Automate guardrails at every stage of the cloud-native application lifecycle and prevent misconfigured K8s resources from being deployed.
Composite Alerts in Kubernetes
Take advantage of powerful composite alert technology from Lacework to comprehensively scan your Kubernetes clusters.
Deliver secure applications on time
Empower developers and DevOps teams to secure applications effortlessly within existing workflows and avoid last-minute security delays.
Uncover hidden runtime threats
Gain immediate visibility into unusual behavior and previously unknown and zero-day threats within K8s and running container workloads.

OUR APPROACH
Comprehensive Kubernetes security
Harden K8s security posture, find vulnerabilities, and automatically detect unusual behavior and runtime threats without writing rules.
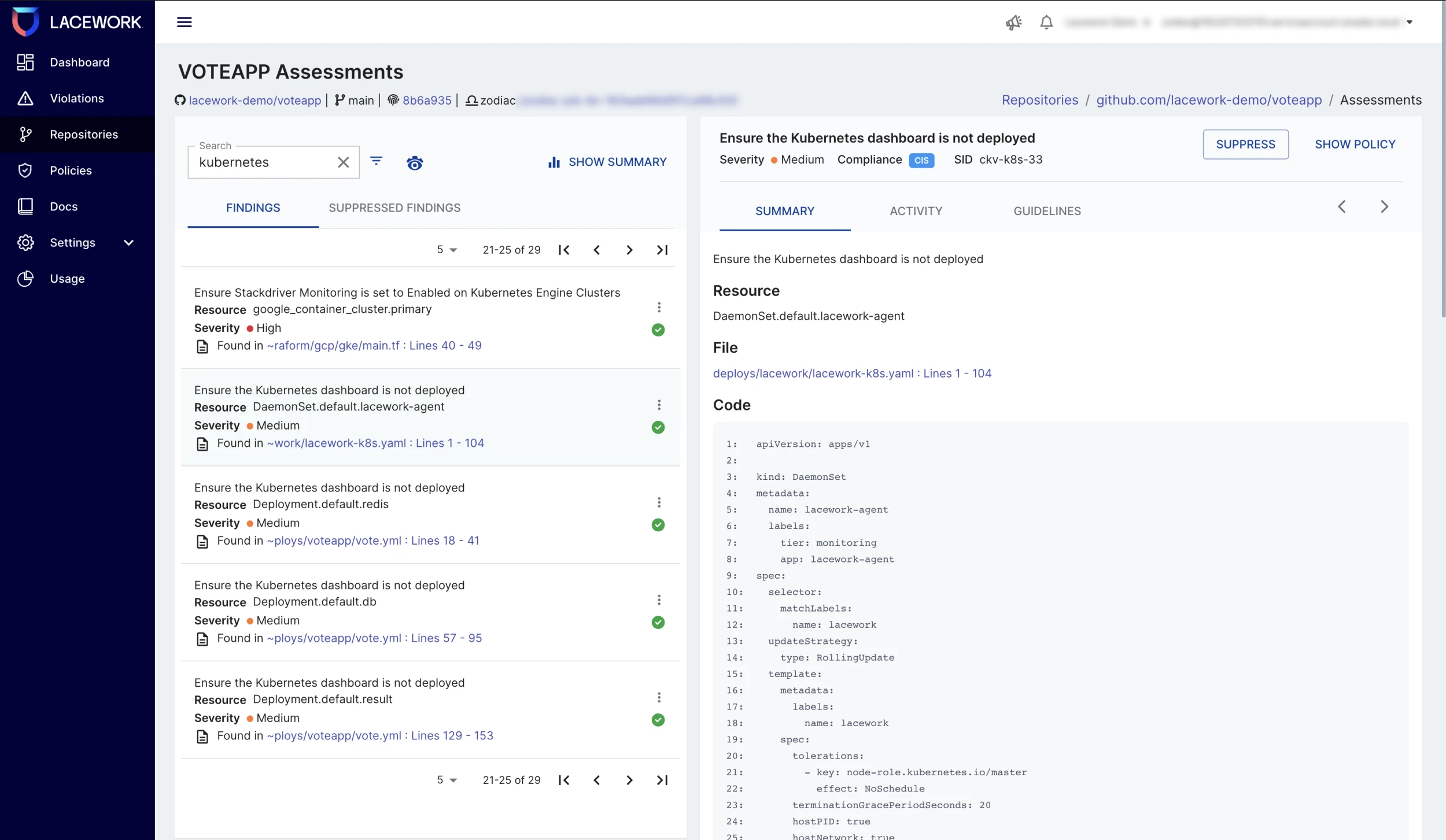
Secure K8s early in software lifecycle
- Rapidly find and fix vulnerabilities and misconfigurations within Kubernetes Manifest, Helm, Terraform, and more.
- Automate security and compliance guardrails at each commit and pull request within GitHub and GitLab repositories.
- Boost developer productivity with actionable findings and guided remediation that are tightly integrated within existing toolchains and workflows.
- Dramatically reduce cloud risk by preventing non-compliant and misconfigured Infrastructure as Code from being deployed.
Focus on image risks that matter most
- Incorporate powerful Composite Alert technology to correlate multiple risk factors and combine build and runtime insights.
- Automatically detect or block non-compliant container images through the Kubernetes Admission Controller before they are deployed.
- Perform fast on-demand scans of container images or schedule every 15 minutes using auto-polling.
- Continuously scan new and existing images within public and private registries.

Harden K8s security posture (KSPM)
- Automatically discover all Kubernetes assets and resources including workloads, pods, nodes, and more.
- Harden security posture (KSPM), enforce least privilege, protect secrets, ensure containers are not running as root, and more.
- Quickly assess compliance with industry best practices and regulations including CIS, HIPAA, ISO, NIST, PCI, and SOC 2.
- Track assets for 90 days and monitor how workloads, RBAC, and other resource configurations drift over time.

Detect threats in Kubernetes runtime
- Continuously monitor node, container, and K8s runtime activity and detect malicious behavior that may indicate container escape, lateral movement, and more.
- Know how K8s clusters, namespaces, and containers are communicating with cloud services, external domains, and other K8s resources.
- Visualize K8s clusters’ network activity, processes, user behavior, and topology with patented Polygraph® technology.
- Get automatic Composite Alerts that combine multiple signals to report on unusual activity; detect unknown threats and zero-day exploits.

Know exactly who is doing what in K8s
- Continuously collect and analyze a massive number of K8s API calls and gain visibility into all user and resource activities.
- Automatically detect user activity, K8s RBAC, deleted resources, authentication errors, forbidden API calls, and more.
- Visualize and trace API calls between the source IP address, K8s, and AWS groups and usernames, target resources, and more.
- Intelligently query Polygraph using multiple terms like actions, namespace, and resource names to focus on specific activity paths.

“Lacework automatically learned how our [Kubernetes] infrastructure worked and started providing insights within hours.”
Nabil Missoum
DEVSECOPS Engineer
Read case study“Implementing Lacework’s platform enabled us to automate our security processes to scale as we grow.”
Mike Parent
Security Engineering Manager
Read case studyFAQs
Kubernetes security prevents internal and external threats from compromising the containers and workloads within your Kubernetes environment. It also quickly detects exploits of vulnerabilities and misconfigurations, and monitors and secures the environment to comply with frameworks and regulations.
Since K8s environments can be challenging to secure given their size, velocity, and ephemeral nature, it is vital to have layered defenses from build through runtime. Effective Kubernetes security offers threat detection, configuration management, and vulnerability checks across the environment.
Implementing Kubernetes security best practices can help with the challenges of securing ephemeral environments. Here is a checklist of ten best practices:
- Monitor and fix IaC at check-in
- Perform container configuration and vulnerability checks at build time
- Use strict roles-based access control (RBAC)
- Harden and isolate nodes and OSes
- Monitor network connections
- Monitor ingress endpoints
- Deploy runtime, agent-based monitoring for host OS and K8s components
- Monitor Kubernetes audit logs
- Monitor deployment of new components and workloads
- Use automation for threat detection
For more information on implementing these recommendations, please check out our eBook: 10 best practices for securing Kubernetes.
Resources & Insights
Featured Insights