Simpler cloud security posture management
Reduce risks and meet compliance requirements without overwhelming your security team.

Old methods can’t match cloud speed
Modern DevOps practices will always outpace outdated, manual security practices.

Disparate tools make visibility difficult
What if, through automation, you could continuously assess security and compliance posture from a single place?
Lack of context can slow down assessments
What if you could prioritize your most harmful misconfigurations and compliance violations based on real world attack behavior?

Proving compliance requires time-consuming processes
What if you could quickly provide security assurance to stakeholders with predefined and custom reports?
EBOOK
CNAPP for Dummies
CNAPP promises to solve key cloud security challenges and break free from years of siloed, unscalable, and inefficient solutions by delivering an integrated and automated approach that combines multiple capabilities — all in a single platform.
Download the eBook
BENEFITS
Stay ahead of risks and compliance
Gain the visibility and context to meet your needs, regardless of how you build, deploy, or orchestrate your cloud resources.
From blind spots to visibility
Inventory your cloud assets and understand when and how your configurations change.
From overwhelmed to prioritized
Pair misconfigurations — including those related to IAM users, policies, and roles — with anomalous activities for better risk context.
From failed audits to new revenue
Prove compliance and unlock opportunities to sell to customers in new regions, industries, and segments.

OUR APPROACH
The platform for CSPM and compliance
Over 75 percent of Lacework customers identified CSPM functionality as their top driver in choosing our platform.
Discover and catalog your cloud resources
- Automatically find, monitor, and inventory all assets across your cloud environment.
- Capture daily inventory to understand changes over time, even if assets no longer exist.
- Use a single platform for all AWS, Azure, Google Cloud, Oracle Cloud Infrastructure, and Kubernetes configurations and gain a consolidated view of your compliance across cloud providers.
- Pair with an agent for deeper telemetry and analysis of workload processes and threats.
Continuously assess risk with pre-built and custom policies
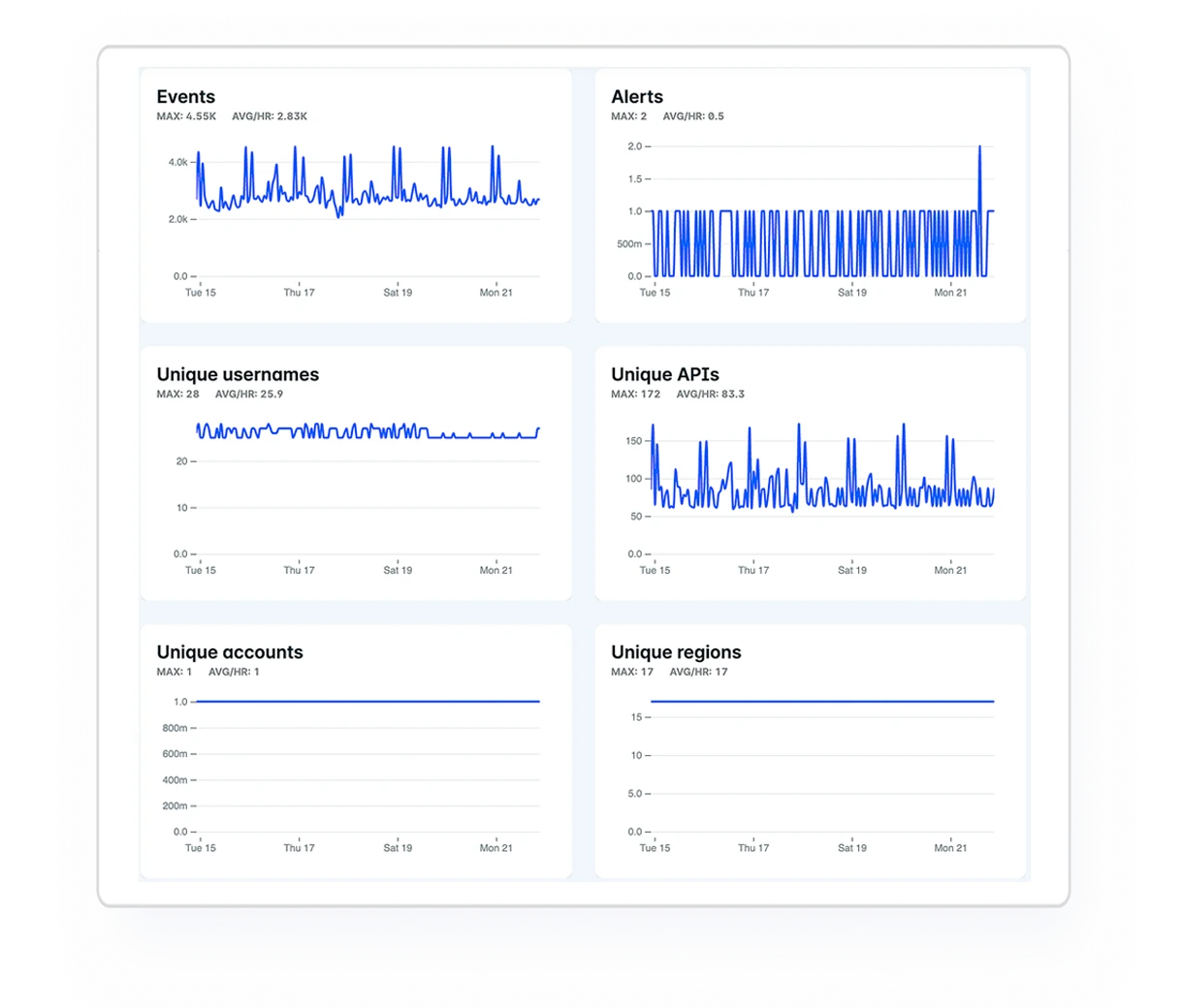
- Automatically monitor and detect misconfigurations and suspicious cloud activity.
- Assess your posture and compliance against hundreds of pre-built policies for standards like PCI, HIPAA, NIST, ISO 27001, SOC 2, and more.
- Set custom policies across cloud providers to meet requirements specific to your organization.
- Get better alert context by assessing risk alongside abnormal user and resource activity like failed logins and IAM escalations.

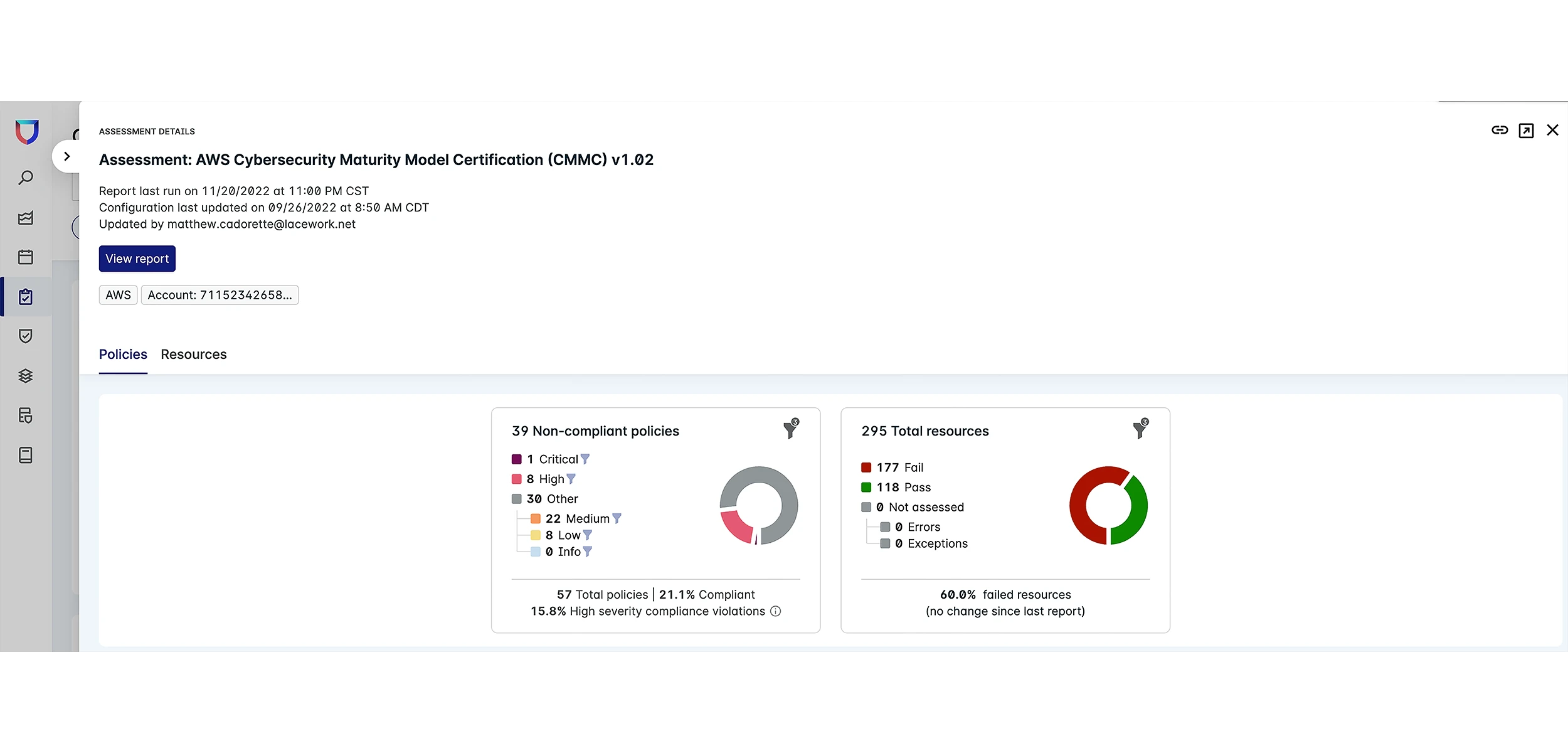
Validate and prove compliance
- See how a specific check applies to all resources across multiple accounts within a cloud service provider via a single dashboard.
- Quickly provide proof and demonstrate your security posture and compliance for customers, partners, and auditors with push-button reports.
- Create custom reports to meet your specific security and compliance needs.
- Get reports in multiple formats like PDF and CSV.
Speed remediation with integrations and guidance
- Get fast alerts when a misconfiguration or compliance violation is surfaced.
- Prioritize alerts and best practice violations with severity and risk scores.
- Use attack path analysis and other context-rich remediation guidance to fix misconfigurations fast.
- Accelerate fixes by integrating with tools like Jira and Slack.


“With Lacework, we have the assurance that an organization’s security posture is continuously being looked at. To do the same thing with other technologies, it takes at least five different tools, which gets expensive and arduous to manage.”
Charlie Gautreaux
Managing Director
"With Lacework, we’ve been able to provide compliance evidence to give partners and regulators the assurance that we’re doing everything that we need to do, and they can see that it’s actually working. Lacework has cut down our workload when it comes to assessments and audits."
John Turner
Senior Security Architect
Read case studyCommon questions about CSPM
A core element of a cloud-native application protection platform (CNAPP), CSPM provides the needed visibility to assess risk properly. This functionality allows you to accurately and continuously assess your risks due to misconfigurations, vulnerabilities, and compliance violations. You can validate your posture against industry best practices and prove compliance with customers, auditors, and others.
It is challenging to build a consistent security and compliance posture due to the ephemeral nature of cloud-native resources. Misconfigurations of cloud assets are common and can expose data or leave you open to attack. In addition, manual security practices and processes cannot keep pace with cloud environments.
Follow this CSPM checklist to build a strong security posture:
- Conduct an inventory of your cloud assets to understand what you have
- Automate security policy controls to prevent misconfigurations and reduce risk
- Validate your security and compliance posture against industry benchmarks and best practices
- Embed checks into developer pipelines by scanning IaC templates for misconfiguration
- Quickly address the most urgent cloud security misconfigurations, so you start your compliance journey with a solid baseline
Resources & insights
Featured Insights



