Amazon Web Services (AWS) cloud security
Build better in the AWS cloud. Continuous security, with automation and fewer rules.

Simplify security for AWS
Existing tools fall short when uncovering misconfigurations, vulnerabilities, and threats. It’s time for a new AWS cloud security approach.
Cloud environments and threats are complex
What if a single platform let you quickly catalog all AWS cloud assets and identify issues with S3 buckets, APIs, access privileges, and more?

Migrating to the cloud can create security gaps
What if you could confidently move new and complex workloads to AWS without worrying about visibility gaps or cloud-specific threats?

Fine tuning security controls is difficult
What if behavioral analytics could automate detection of zero days, account compromise, and other threats?

Getting audit-ready takes time and money
What if you could continuously track changes across your AWS cloud to easily report compliance with SOC 2, HIPAA, PCI, CIS Benchmarks, and more?

BENEFITS
Go further, faster in the AWS Cloud
Lacework Polygraph® Data Platform provides the visibility needed to reduce security risk, detect threats, and demonstrate compliance across your AWS environment.
Built for the way you work in AWS
Go further, faster by integrating security into existing tools and workflows.
Securing end to end as you build
Go further, faster with a complete view into the compliance, risks, and threats across cloud accounts and workloads.
Monitoring activity across your AWS Cloud
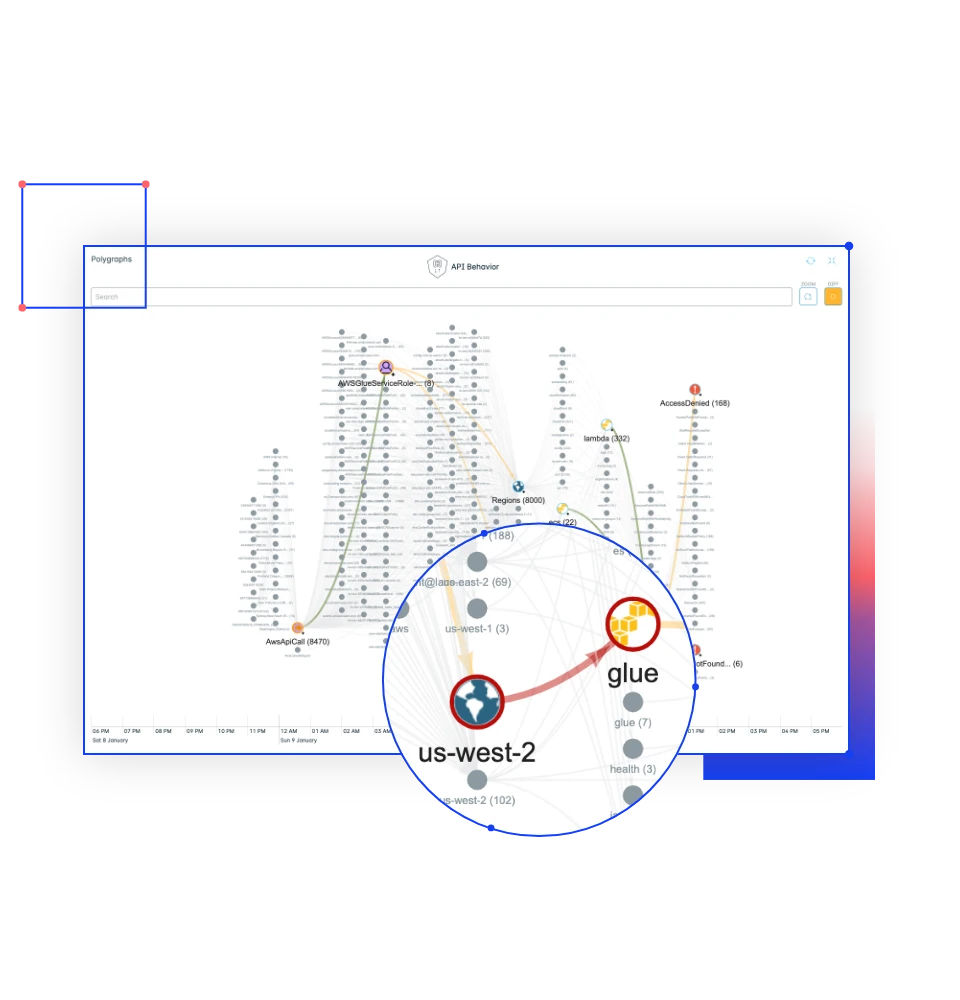
Go further, faster by automatically analyzing AWS CloudTrail with our patented behavior analytics to uncover anomalous activity and unknown threats.
Insights to act faster
Go further, faster with context-rich alerts and browsable activity graphs that help you investigate and respond quickly.

Integrations
As part of the shared responsibility model, we believe it is important to maximize the value you get from the cloud. There are elements of cloud security you’re accountable for and Lacework can help. Here’s how Lacework supports and integrates with AWS:
Operating Systems
- Amazon Linux 2
- Amazon Linux 2023
Applications
- Amazon EKS
- Amazon ECS
- AWS Fargate
- AWS Graviton
- Amazon EC2
- AWS CloudFormation
- AWS CDK
- AWS Control Tower
- Amazon Guard Duty
Data
- AWS Cloud Trail
- AWS Security Hub
- Amazon Eventbridge
- AWS Lambda
- Amazon CloudWatch
OUR APPROACH
A data-driven approach simplifies AWS cloud security
Lacework ingests and analyzes your cloud data to automatically detect misconfigurations and anomalies.
Build modern applications securely
- Continuously monitor vulnerabilities and misconfigurations
- Analyze AWS CloudTrail logs for user, app, process, and network behavior
- Use patented behavioral analytics to uncover escalation of privileges
- Surface cloud misconfigurations like open S3 buckets
- Check environment against cloud best practices and compliance requirements
Secure your containers
- Reach deeper into the compute layer to protect services
- Understand critical security events within Kubernetes clusters
- Gain visibility into EC2 instances with our agent
Battle ransomware in the AWS Cloud
- Uncover anomalous activity that could signal a need for investigation before a ransomware attack
- Learn best practices to mitigate the risks associated with ransomware
- Avoid alert fatigue by surfacing only the most critical risks
- Solve issues quickly by using ticketing, messaging, and workflow integrations
“It’s much easier to centralize our entire alerting system. It also reduced alert fatigue and streamlined the alert whitelisting process. Lacework learns the rules changes as they come. I can spend my time fixing real issues instead of fixing the whitelisting.”
Maxime LeBlanc
Information Security Specialist (SECOPS)
Read case studyResources & Insights
Featured Insights


