Cloud infrastructure entitlement management
Reduce cloud identity risk by knowing your users and their access, pinpointing which are riskiest, and right-sizing their entitlements
Who holds the keys to your cloud?
Pressure to innovate rapidly leaves many identities over-permissioned. And with low visibility, you can’t fully see where you’re at risk.

You don’t know who your users are
Thousands of user and service identities, and tens of thousands of possible permissions, make manual entitlement audits impossible.
You don’t know what your users need
Most cloud identities are over-permissioned. But are you sure your “fix” isn’t going to block developers and break applications?
You don’t know which issues to fix first
Finding over-permissioned cloud identities is essential but relatively useless without knowing which pose the greatest risk.
ESG Research
Cloud Entitlements and Posture Management Trends
The report compiles key survey findings and trends around the adoption and implementation of cloud security posture management (CSPM) and cloud infrastructure entitlement management (CIEM) solutions by organizations to reduce their cloud risks.
Read Here
Benefits
From identity crisis to identity control
Time to get identities in order. Know what users can do and understand what they need. Then fix critical risks without breaking anything.
Know your users and their permissions
Security starts with clear visibility. Lacework identifies who can perform which actions and continuously discovers new entities and their permissions.
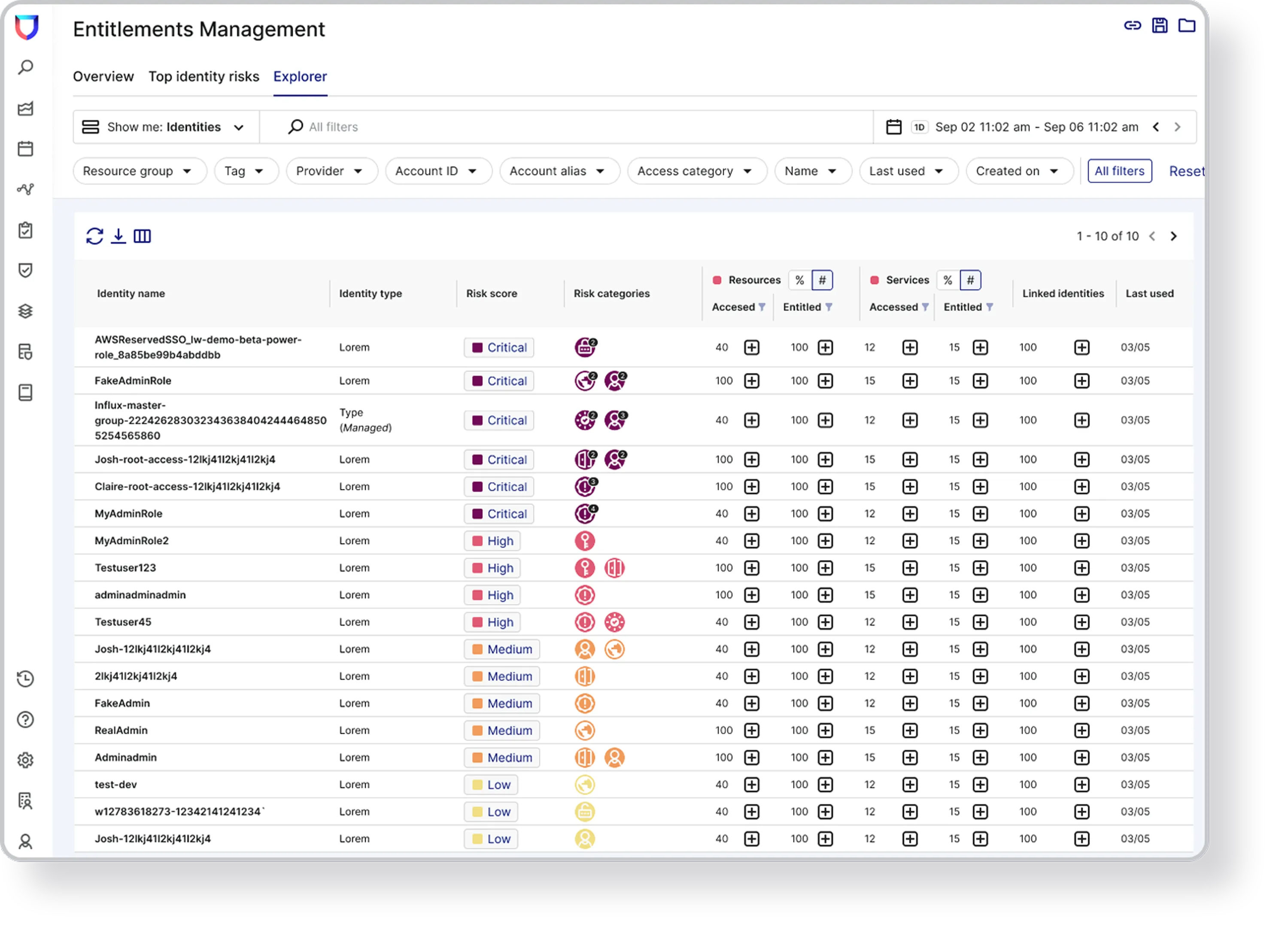
Pinpoint your riskiest entities
Understand which identities are overly-permissive. Automatically see exactly which users and services pose the greatest risk and prioritize them first.
Right-size with confidence
See which identities and permissions are rarely, if ever, used. Then scope down entitlements using auto-generated recommendations without damaging trust.

Our Approach
Least privilege for all your cloud entities
Monitor identities and entitlements. Locate excessive permissions. Pinpoint entities that pose the greatest risk. Suggest right-sized policies.
Discover entities and their permissions
- Dynamically discover and enumerate all user, resource, group, and role identities
- Correlate identity and resource permissions, permission boundaries, SCP, trust policy, and more
- Monitor activity and linked identities that can assume an entity’s privileges and vice versa
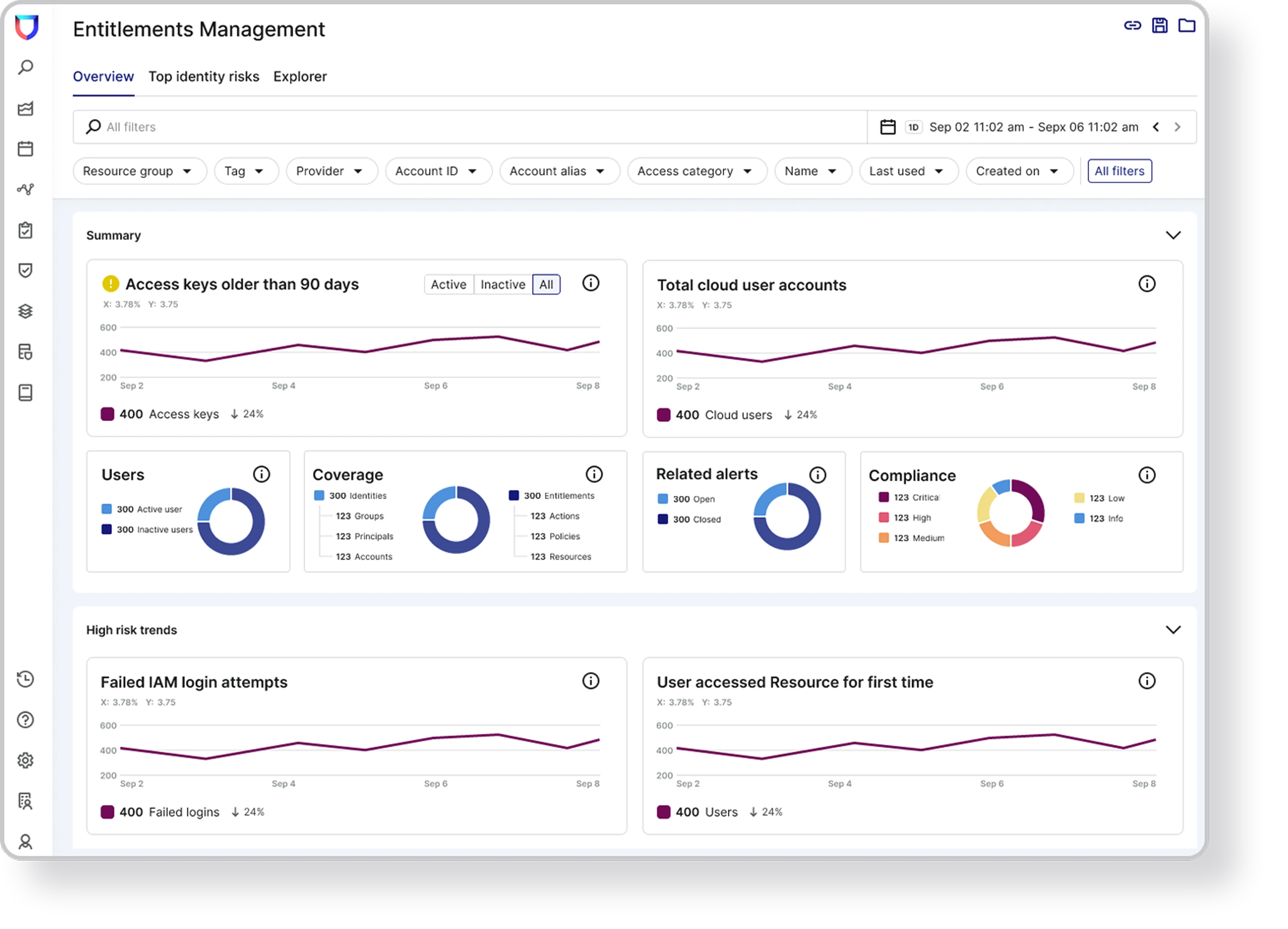
Observe usage to find over-privileged entities
- Continuously monitor entities and permissions to understand their usage patterns
- Uncover excessive permissions by combining event data with account configuration data
- Identify sensitive resources, like RDS, that can be accessed by an excessive number of entities

Prioritize the riskiest identities
- Use risk scores that consider usage, role chaining, toxic combinations, secrets, and more
- Visualize attack paths for entities with permissions to high-value resources, like S3 and RDS
- Pinpoint the handful of identities that make the biggest impact in reducing attack surface risk
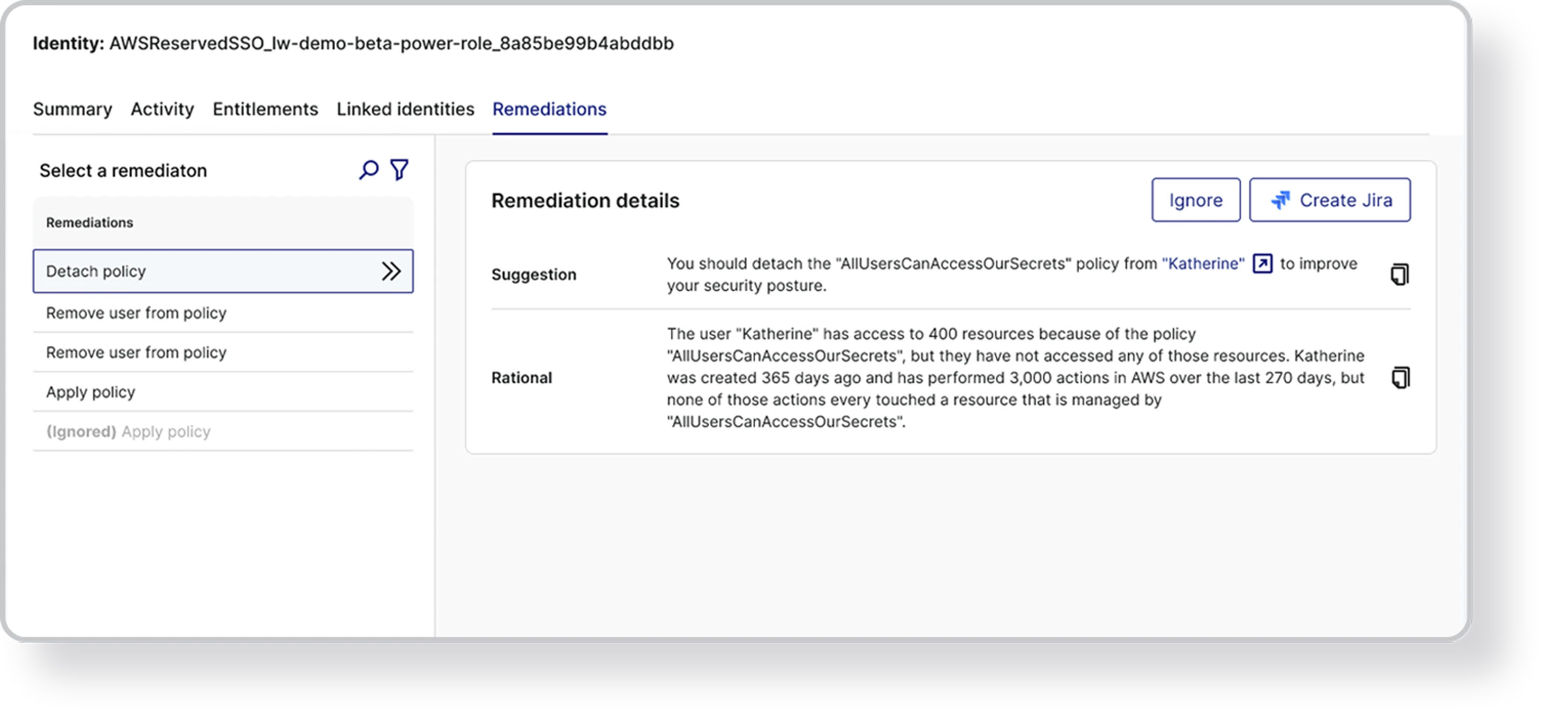
Get suggestions for right-sizing policy
- Receive guidance for reducing permissions based on risk and historical usage
- Gain detailed observability evidence that provides the logic for each suggested policy change
- Revoke excessive and unused privileges, update policy conditions, and reduce identity risk
“I feel comfortable knowing we have very few blind spots in our cloud environment. Lacework stretches our visibility so far that I feel I can see everything.”
Kevin Tham
CISO
Read case study
“We want to make sure that everything in our cloud environments is visible, and that we can audit it. Lacework has helped with both visibility and auditing, which has really allowed us to grow and mature, and enabled our teams to generate value.”
Steve Lukose
Director of Security Engineering
Read case study
“With the reports generated by the Lacework dashboard, we can easily see what resources are compliant, what resources are not compliant, and what we need to do to achieve compliance.”
Jay Rawal
Devops Engineer
Read case studyFAQs
Cloud infrastructure entitlement management, or CIEM (pronounced “kim”), is a cloud security solution that focuses on helping organizations enforce the principle of least privilege when building, deploying, using, and managing cloud infrastructure services. A CIEM security platform is designed to help with cloud identity governance and to right-size permissions that may be excessive and dormant, ensuring that each cloud entity has the minimum level of access necessary to perform its job.
Cloud infrastructure entitlement management provides centralized visibility and control by offering a centralized platform for monitoring, managing, and auditing who has access to what within Amazon Web Services (AWS), Microsoft Azure, and Google Cloud, and whether these permissions are appropriate. CIEM helps organizations identify and mitigate excessive permissions and “cloud identity debt” (i.e., the buildup of unused identities and excessive privileges accumulated over time).
For an in-depth look at CIEM and its importance, read this blog.
Cloud infrastructure entitlement management, focuses on cloud identity governance, and managing user and service privileges related to the use of cloud services. It helps identify over-privileged access, excessive permissions, and unused entitlements, reducing the risk of security breaches. CIEM is a part of privileged access management, ensuring only the right individuals have access to critical resources.
On the other hand, CSPM, cloud security posture management, focuses on compliance and risk management. It involves identifying and remediating risks associated with IAM-related misconfigurations such as weak/default passwords, hardcoded secrets, wildcard permissions, no MFA, and more.
Although both CIEM and CSPM are crucial for cloud security, their focus areas differ. CIEM manages what actions users and services can take, while CSPM assesses the configuration of cloud services with frameworks and best practices. Both contribute to a comprehensive cloud security strategy.
Both CIEM and the CNAPP contribute significantly to cloud security, but they play different roles. CIEM is centered around privileged access management, ensuring that the correct individuals or services have appropriate access in a cloud environment. It identifies over-privileged access and unused entitlements, thus reducing security risks.
CNAPP, on the other hand, is designed to holistically secure cloud-native applications. It is a superset of integrated cloud security capabilities that provide artifact scanning, risk assessments, and threat detection across each stage of the cloud-native application lifecycle.
The relationship between CIEM and CNAPP is symbiotic. CIEM is very much a part of CNAPP. CIEM is a key component of CNAPP, as it manages entitlements and secures privileged access. Together, they form a robust cloud security strategy.
Resources & Insights
Featured Insights
See Lacework in action
Watch on-demand demos to discover how you can automate security and compliance across AWS, Azure, Google Cloud, and private clouds with Lacework.