A guide to navigating vulnerability management
Table of contents
What is vulnerability management? Why implement vulnerability management? A guide to the vulnerability management process Automating vulnerability management Vulnerability management vs vulnerability assessment Key considerations for selecting a toolIn the ever-evolving landscape of cybersecurity, the importance of vulnerability management cannot be overstated. As an integral process of identifying, assessing, and resolving system vulnerabilities, vulnerability management offers a proactive approach for organizations to stay ahead of potential threats, reduce the risk of security breaches, and maintain compliance with industry regulations. This guide will delve into what vulnerability management is, its benefits, the difference between vulnerability management and vulnerability assessment, and factors to consider when selecting a suitable solution for your organization.
What is vulnerability management?
At its core, vulnerability management is a systematic process of identifying, assessing, and mitigating security vulnerabilities within systems and networks. With the rising complexity of cyber-attacks and the constantly evolving threat landscape, it is critical for organizations to stay vigilant. A robust vulnerability management program significantly reduces risk exposure and minimizes the impact of potential security breaches by continuously scanning systems and networks, assessing vulnerabilities based on severity and impact, and implementing an efficient remediation process.
Why implement vulnerability management?
The implementation of vulnerability management offers numerous benefits to an organization's overall security and risk reduction efforts. The most significant advantage is the enhanced security posture achieved by proactively identifying and addressing vulnerabilities. Regular vulnerability scans and assessments ensure that your organization stays ahead of potential threats, thereby maintaining a secure infrastructure. Furthermore, vulnerability management significantly reduces the risk of data breaches by quickly remediating vulnerabilities, minimizing the chances of unauthorized access to sensitive data, and helping organizations meet regulatory compliance requirements, such as GDPR and PCI DSS.
A guide to the vulnerability management process
Adopting a structured vulnerability management process enables organizations to identify, prioritize, and remediate vulnerabilities systematically. This process encompasses identifying and categorizing vulnerabilities, assessing them based on risk level, and developing a plan for remediation. Regular monitoring of the vulnerability remediation progress is crucial to ensure timely resolution and prevent new issues.
A robust vulnerability management process is crucial for maintaining the security of your environment. It helps identify and address potential vulnerabilities before they can be exploited by attackers. By streamlining your vulnerability management efforts, you can significantly enhance your security posture. This includes gaining real-time visibility into your environment, leveraging proactive threat intelligence, and automating remediation workflows.
Automating vulnerability management
In the fast-paced world of cybersecurity, automating vulnerability management can significantly streamline the process and enhance security posture. Automation eliminates the manual efforts required for scanning and identifying vulnerabilities, ensuring timely detection and remediation. Additionally, automation in vulnerability management offers real-time information about vulnerabilities, allowing organizations to prioritize and remediate based on severity and potential impact. When implementing automation, it's essential to establish a vulnerability management program with clear policies and procedures. This includes regular assessment and prioritization of vulnerabilities based on potential impact, allowing organizations to focus their resources on addressing critical vulnerabilities first.
Vulnerability management and vulnerability assessment: A comparative analysis
While often used interchangeably, it's essential to understand the differences between vulnerability management and vulnerability assessment. Vulnerability assessment focuses on identifying and quantifying system vulnerabilities, providing a comprehensive report on potential weaknesses. On the other hand, vulnerability management takes a holistic approach, covering the entire vulnerability lifecycle, including detection, prioritization, remediation, and ongoing monitoring. It ensures that vulnerabilities are not just discovered but promptly addressed, establishing a proactive security stance and minimizing the risk of cyberattacks.
Key considerations for selecting a suitable vulnerability management solution
When selecting a vulnerability management solution, organizations should consider scalability, flexibility, integration with existing security infrastructure, and robust reporting and analytics capabilities. The solution should scale with your needs, be easily customizable, and integrate seamlessly with existing tools, such as your security information and event management (SIEM) platform. Additionally, it should provide comprehensive and customizable reports, advanced analytics capabilities, and adhere to industry standards and compliance regulations. By considering these factors, organizations can select a solution that meets their specific needs and effectively mitigates risks.
INTERACTIVE DEMO
Lacework custom vulnerability score
Jump into the Lacework platform and see how we assign vulnerabilities a propriety risk score, based on relative risk to your unique environment.
Access the demo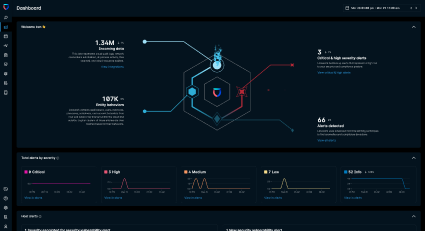
This article was generated using automation technology. It was then edited and fact-checked by Lacework.