What is the principle of least privilege in cybersecurity?
Table of contents
The details of the principle of least privilege Implementation approaches Benefits of the principle of least privilege Overcoming challenges in implementation The principle of least privilege and zero trust security Which tools can help implement least privilegeAt the core of modern cybersecurity, we find the principle of least privilege (PoLP), a critical concept that aims to mitigate the potential damage caused by unauthorized access or privilege abuse. But what is the principle of least privilege? In essence, it's about granting users the bare minimum level of access required to perform their functions, not a smidge more. By restraining user privileges, businesses can reduce the risk of accidental or intentional misuse of sensitive information, decrease the impact of security breaches, and strengthen overall system security.
Diving into the details of the principle of least privilege
The principle of least privilege (PoLP) is a security doctrine that underscores the importance of limiting user access rights to the bare minimum necessary for their roles. It's founded on the idea that users should have only the necessary set of privileges to fulfill their tasks, nothing extra.
By implementing the principle of least privilege, businesses can reduce the risk of unauthorized access, data breaches, and potential damage caused by insider threats. This principle plays a crucial role in ensuring that each user has access only to the resources and information required for their distinct roles.
Adopting the principle of least privilege is crucial for maintaining a robust security posture. By granting users only the permissions they need, businesses can limit the potential fallout of a security breach. Even if an attacker successfully infiltrates a user's account, the damage they can cause is constrained due to the absence of excessive privileges.
Furthermore, the principle of least privilege enhances security by reducing the attack surface. By controlling user access rights, businesses can decrease the number of potential entry points for attackers. This helps in reducing the risk of unauthorized actions and impedes the lateral movement of attackers within the network.
Approaches to implement the principle of least privilege
Implementing the principle of least privilege is key to maintaining a strong security stance within an organization. By assigning users only the minimum level of access required to carry out their tasks, you can effectively lower the risk of unauthorized access and potential data breaches. Let's explore some best practices and steps for successful implementation.
Best practices for implementing the principle of least privilege
1. Evaluate user roles and permissions: Start by reviewing and documenting the specific access needs for every user role within your organization. This will assist you in identifying unnecessary privileges and potential security threats.
2. Adopt an Identity and Access Management (IAM) system: An IAM system can simplify user provisioning, ensure proper authentication, and make managing user privileges easier.
3. Regularly refresh user access permissions: Regularly review and modify user access permissions based on changing roles, responsibilities, or project needs. This will help uphold the principle of least privilege over time.
Steps to implement the principle of least privilege
1. Identify and categorize resources: Start by identifying and categorizing your organization's resources, including databases, servers, applications, and files. Categorizing resources will help you determine the appropriate access levels for different user roles.
2. Define user roles and access levels: Formulate clear user roles and define the access levels associated with each role. This will ensure that users have only the necessary permissions to perform their tasks.
3. Assign permissions based on user roles: Allocate appropriate permissions to each user role based on their distinct responsibilities. Avoid granting excessive privileges and regularly review and adjust permissions as necessary.
Key considerations for successful implementation
1. Employee training and awareness: Provide comprehensive training to employees on the principle of least privilege and its importance in maintaining a secure environment. This will help promote a security-conscious culture within your organization.
2. Regular auditing and monitoring: Set up a system for auditing and monitoring user activities and access privileges. This will help spot any unauthorized actions or potential security vulnerabilities.
3. Collaboration with IT and security teams: Ensure collaboration between IT, security, and business teams to establish effective policies, procedures, and controls for implementing and maintaining the principle of least privilege.
Benefits of the principle of least privilege
The principle of least privilege delivers numerous advantages for organizations, ranging from enhanced security and reduced risk of data breaches to improved regulatory compliance.
One of the primary benefits of implementing the principle of least privilege is the improved security it affords. By granting users only the minimum level of access required to perform their tasks, businesses can effectively limit the potential damage caused by insider threats or external attackers. This approach significantly reduces the attack surface, making it harder for malicious actors to exploit vulnerabilities and gain unauthorized access to sensitive data.
The principle of least privilege also provides protection against privilege creep, a phenomenon where users gradually accumulate excessive privileges over time, as they are granted additional access rights without proper monitoring or evaluation. By adhering to the principle of least privilege, businesses can prevent this phenomenon, ensuring that users only have the necessary privileges for their specific roles and responsibilities.
Beyond enhanced security and protection against privilege creep, the principle of least privilege can also contribute to improved regulatory compliance. Many industry-specific regulations, such as the General Data Protection Regulation (GDPR) or the Payment Card Industry Data Security Standard (PCI DSS), stress the importance of implementing least privilege as a fundamental security measure. By adhering to this principle, businesses can demonstrate their commitment to data protection and regulatory compliance.
Overall, the principle of least privilege serves as a crucial element of a comprehensive security strategy, offering increased security, reduced risk of data breaches, protection against privilege creep, and improved regulatory compliance.
Overcoming challenges in implementing the principle of least privilege
Although the principle of least privilege (PoLP) is paramount for maintaining a robust security posture, businesses often encounter challenges when trying to implement it effectively.
1. Identifying and managing user access rights: With a large number of users and complex access control systems, keeping track of who has access to what resources can be challenging. Businesses need to carefully define and assign access rights based on job roles and responsibilities to ensure that users only have access to the resources they need to perform their tasks.
2. Balancing security with user productivity: Finding the right balance between security and user productivity can be challenging. Restricting user access to minimize risks can sometimes hinder productivity. It is essential to strike a balance by implementing strong security measures while providing users with the necessary access to perform their job effectively.
3. Overcoming resistance to change within the organization: Resistance to change is a common challenge when implementing any new security measures. Employees may resist the changes introduced with the principle of least privilege due to concerns about increased complexity or potential disruption to their work. To overcome this resistance, businesses need to communicate the benefits of PoLP, provide training and support, and involve employees in the decision-making process.
By tackling the aforementioned obstacles, organizations can effectively adopt the principle of least privilege, bolstering their security measures. Comprehensive solutions are available that support organizations in surmounting these hurdles, facilitating the successful application of PoLP strategies.
The principle of least privilege in the context of zero trust security
The principle of least privilege (PoLP) is a key concept in cybersecurity that aligns perfectly with the zero trust security model. Zero trust is a strategy that assumes no trust in any user or device, regardless of their location relative to the network perimeter. It requires continuous verification and validation of all users and devices attempting to access resources.
By integrating the principle of least privilege within a zero trust architecture, businesses can significantly improve their security posture. Least privilege access controls ensure that users and devices are granted only the minimum level of access necessary to perform their tasks. This means that even if a user's credentials are compromised, the attacker would have limited access and be unable to move laterally within the network.
Implementing least privilege access controls in zero trust architectures provides businesses with granular control over user permissions. It allows administrators to define and enforce access policies based on individual roles, responsibilities, and the principle of least privilege. This approach reduces the attack surface by minimizing the potential damage that can be caused by insider threats, privilege escalation, or unauthorized access.
The combination of least privilege and zero trust offers several benefits for enhanced security. Firstly, it reduces the risk of data breaches and unauthorized access by ensuring that users have only the necessary permissions to perform their duties. Secondly, it helps businesses comply with regulatory requirements by implementing strong access controls and user segregation. Lastly, it improves overall operational efficiency by streamlining access management and reducing administrative overhead.
Utilizing tools and technologies for implementing the principle of least privilege
Implementing the principle of least privilege is vital for maintaining a secure and resilient system. Thankfully, there are several tools and technologies available that can assist businesses in enforcing this principle effectively.
Role-based access control (RBAC) is a crucial instrument in implementing the principle of least privilege. RBAC allows organizations to designate specific roles to users based on their responsibilities and job functions. By providing users only the necessary privileges required to perform their tasks, RBAC ensures that individuals can access the resources they need without jeopardizing security. The feature of RBAC allows organizations to specify detailed access controls, ensuring that users are granted the appropriate level of access to resources.
Privileged Access Management (PAM) Solutions play a crucial role in supporting the principle of least privilege within organizations. These systems help in overseeing and regulating accounts with elevated permissions, such as administrator or root access, which carry significant security risks due to their high level of access. The adoption of PAM helps companies to apply stringent access protocols, oversee privileged operations, and reduce the threat of unauthorized entry. By leveraging these capabilities, organizations can achieve a robust management and auditing process for privileged accounts, guaranteeing that sensitive resources are accessible only to approved personnel.
For businesses adopting cloud-native architectures, security platforms that support least privilege access are essential. These platforms provide visibility and control over cloud resources, allowing businesses to enforce granular access controls and monitor user activities. One such platform offers robust access control mechanisms, including Just-in-Time (JIT) access, which enables businesses to grant temporary access to resources only when needed, further reducing the attack surface.
INTERACTIVE DEMO
Lacework CIEM guided tour
Learn how Lacework can help you jumpstart the principle of least privilege in your cloud accounts.
Access the tour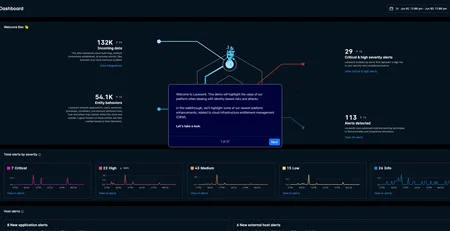
This article was generated using automation technology. It was then edited and fact-checked by Lacework.