Understanding cloud infrastructure entitlement management (CIEM)
Table of contents
The role of CIEM Key elements of CIEM CIEM applications CIEM's role in improving cloud security Key security advantages of CIEMCloud infrastructure entitlement management (CIEM) plays a pivotal role in a robust cloud security strategy. As businesses transition more operations to the cloud, the task of managing access rights and permissions grows more complex. CIEM provides a unified solution to manage entitlements effectively, ensuring secure access to cloud resources.
CIEM offers visibility into user entitlements, permissions, and access patterns across your cloud infrastructure. It aids in identifying and mitigating security risks, enforces the principle of least privilege, and monitors user activities. By integrating CIEM into your cloud security strategy, you can bolster your overall security posture and protect your critical data from unauthorized access.
The role of CIEM in your cloud security strategy
The significance of cloud security cannot be overstated in our digital era. With more organizations migrating their operations to the cloud, they face a myriad of security challenges. Ensuring the protection of sensitive data, maintaining compliance with industry regulations, and safeguarding against cyber threats are top priorities for any business.
One critical aspect of cloud security is entitlement management, which involves controlling and monitoring user access to resources and data within the cloud environment. The risks associated with improper entitlement management are significant, potentially leading to data breaches, unauthorized access, and compliance violations.
Here's where Cloud Infrastructure Entitlement Management (CIEM) steps in. CIEM is a specialized solution designed to mitigate the risks associated with entitlement management in the cloud. By offering a comprehensive view of user entitlements across multiple cloud platforms, CIEM enables organizations to identify and mitigate potential security gaps and vulnerabilities.
CIEM extends beyond traditional Identity and Access Management (IAM) solutions by offering granular visibility and control over user entitlements, permissions, and configurations in the cloud. It supports organizations in enforcing the principle of least privilege, ensuring that users have access only to the resources they need.
In addition, CIEM continuously monitors and audits user entitlements, detecting and alerting on any suspicious activities or policy violations. This proactive approach allows organizations to respond quickly to potential security incidents, preventing them from escalating into serious breaches.
By incorporating CIEM into your cloud security strategy, you can enhance your overall security posture, reduce the risk of data breaches, and ensure compliance with industry regulations.
Key elements of CIEM
CIEM (Cloud Infrastructure Entitlement Management) is a vital solution for comprehensive cloud security, safeguarding your organization's sensitive data and resources. To implement this powerful security measure effectively, it is essential to understand the key components of CIEM.
One of the primary components of CIEM is Identity and Access Management (IAM). IAM enables organizations to manage user identities and control their access to various cloud resources. With IAM, you can assign roles and permissions to users, ensuring that only authorized individuals have access to sensitive data.
Entitlement discovery and analysis are also crucial components of CIEM. This feature assists organizations in identifying and analyzing the entitlements associated with different users and resources. By gaining visibility into these entitlements, organizations can better understand their security posture and identify potential vulnerabilities or risks.
CIEM applications
CIEM, or Cloud Infrastructure Entitlement Management, is a potent tool for organizations looking to enhance their cloud infrastructure's security. By employing CIEM, businesses can gain improved visibility and control over user access and permissions, thereby reducing the risk of unauthorized access and data breaches.
One key application of CIEM is in implementing cloud infrastructure. CIEM allows organizations to manage and govern user access across various cloud platforms, ensuring that only authorized users have necessary privileges. This helps prevent unauthorized access, insider threats, and potential security breaches.
Another important aspect of CIEM is its capability to integrate with existing security tools. CIEM solutions can seamlessly integrate with other security tools, such as identity and access management systems and security information and event management (SIEM) solutions. This integration enables organizations to leverage their existing security infrastructure, enhancing its capabilities and providing a more comprehensive and robust security posture.
When implementing CIEM, it is crucial to follow best practices to ensure its effectiveness. These include regularly reviewing and updating access policies, conducting regular audits and risk assessments, and implementing multi-factor authentication. Additionally, organizations should consider leveraging automation and machine learning capabilities offered by CIEM solutions to streamline security operations and improve incident response.
At Lacework, our CIEM solution is designed to provide advanced security and compliance capabilities for cloud environments. With our CIEM platform, organizations can implement and manage CIEM across their cloud infrastructure easily, integrate it with existing security tools, and follow best practices to enhance their security posture. Contact us today to learn more about how our CIEM solution can help secure your cloud environment.
CIEM's role in improving cloud security
CIEM, or Cloud Infrastructure Entitlement Management, plays a vital role in enhancing cloud security by reducing the attack surface and providing enhanced visibility and control over cloud environments. With CIEM, organizations can better protect their sensitive data and mitigate the risks associated with cloud-based operations.
One of the main benefits of CIEM is its ability to minimize the attack surface. By continuously monitoring cloud infrastructure, CIEM identifies and eliminates excessive permissions, misconfigurations, and vulnerabilities that malicious actors could exploit. This proactive approach ensures that only authorized individuals have access to sensitive resources, significantly reducing the risk of unauthorized access and data breaches.
Additionally, CIEM enhances visibility and control over cloud environments. It provides organizations with a comprehensive view of their cloud infrastructure, including user entitlements, privileges, and activity logs. This visibility enables security teams to quickly identify and address any security gaps or suspicious activities, ensuring a more robust and secure cloud environment.
With CIEM, organizations can also enforce least privilege access policies, granting users only the permissions they need to perform their specific tasks. This granular control helps minimize the potential impact of insider threats or compromised credentials, further strengthening cloud security.
Overall, CIEM is an essential tool for organizations looking to improve their cloud security posture. By reducing the attack surface and enhancing visibility and control, CIEM enables businesses to protect their sensitive data, maintain compliance with industry regulations, and confidently embrace the benefits of cloud computing.
Key security advantages of CIEM
When it comes to protecting your organization's sensitive data and maintaining compliance, CIEM (Cloud Infrastructure Entitlement Management) offers a range of key security benefits. With CIEM, you can ensure that the right individuals have the correct access to your cloud resources, reducing the risk of unauthorized access and potential data breaches.
One of the core features of CIEM is role-based access control. This feature allows you to define specific roles and permissions for different users or groups within your organization. By assigning roles based on job responsibilities, you can enforce the principle of least privilege and limit access to only what is necessary. This helps minimize the attack surface and reduces the chances of internal threats.
Real-time alerting and monitoring are another crucial aspect of CIEM. With CIEM, you can proactively monitor user activities, access patterns, and entitlement changes in real-time. This enables you to detect any suspicious or unauthorized activities promptly. By setting up alerts, you can be instantly notified of any potential security risks, allowing you to take immediate action to mitigate them.
In addition to role-based access control and real-time monitoring, CIEM also provides robust compliance and audit support. CIEM solutions offer comprehensive visibility into access entitlements, helping you meet regulatory requirements and pass audits. With detailed audit logs and reports, you can easily demonstrate compliance to auditors and stakeholders.
By leveraging CIEM, you can strengthen your organization's security posture, protect sensitive data, and meet compliance obligations. At Lacework, we offer an advanced CIEM platform that combines these key security benefits with ease of use and scalability. Contact us today to learn how our CIEM solution can help safeguard your cloud infrastructure.
INTERACTIVE DEMO
Lacework CIEM
In this guided demo, get an interactive look at Lacework cloud infrastructure entitlement management (CIEM).
Access the tour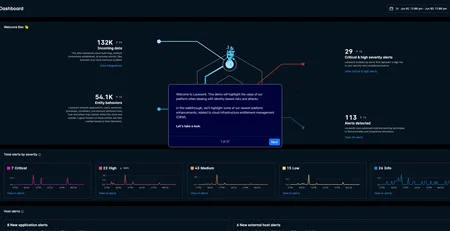
This article was generated using automation technology. It was then edited and fact-checked by Lacework.