Don’t waste your time following these 3 password security rules
 You forget your password. It happens to all of us—you type in your credentials, but then get an error saying it’s wrong. You try again, still wrong. Then you try to reset the password, and you see the message, “Password can’t be the same as your existing password.” 😤
You forget your password. It happens to all of us—you type in your credentials, but then get an error saying it’s wrong. You try again, still wrong. Then you try to reset the password, and you see the message, “Password can’t be the same as your existing password.” 😤
It’s very frustrating; and that frustration is what leads us to make not-so-great decisions when choosing passwords. On top of that, there’s an overwhelming amount of password guidance out there. If you’re like me, you’re probably not listening to all of it—it’s too much to keep up with. But I have some good news: not all password-related recommendations are hard-and-fast rules. Some of the rules are only applicable to you in certain situations, which means that you shouldn’t waste your time abiding by them. Here are three common password rules that I’ve learned are okay to break (sometimes).
- You should never write down your passwords on paper.
Writing down your passwords on a Post-It and sticking it on your screen is bad, right? Actually, it depends. If you do this in a company office where a bunch of different people walk by and have access to your workspace, then writing down your passwords and leaving them in the open is a bad idea. But if you work from home and only you and your family use your office, it might be worth the trade off. The chances of someone breaking into your home, going straight to your computer, and using your sticky note to find the password and log in is pretty slim. Hopefully no one breaks into your home, but if they do, they’re probably going to target physical valuable objects, like your wallet, jewelry, or electronics. Cybercriminals have better (and easier, for them) ways to get into your computer. If it’s your data they want, they have the skills to hack into your computer from the comfort of their own homes. Writing down your passwords on a Post-It is actually a lot safer than it is to reuse the same passwords on all your accounts or to store them in a file on your desktop. It’s much more likely that hackers will get your passwords that way. So, if writing down your password on sticky notes saves you from resetting your password every time you log in to a certain site, go ahead and do that.
- You need to mask your passwords so no one steals them.
Many websites and applications “mask” passwords, which means that they hide the characters on the screen as you type them. The idea behind this is that no one around you will be able to see the password you’re typing. But how often is someone actually standing behind you while you’re entering a password? We’re usually either at home, in an office or cubicle, or just sitting somewhere without someone directly peering over our shoulder. And if someone really wanted to find your password, they could watch to see which keys you press and figure it out that way. Cybercriminals have the skills and technology, like keylogging, to track your password regardless of whether anyone can see it. In reality, masking passwords introduces more problems than it solves. Users actually make more mistakes when they can’t see what they’re typing, prompting them to reset their passwords when they didn’t really need to. And they’re more likely to use simple passwords that they’re confident typing—but as we know, simple passwords are easy to hack. We’re seeing increasingly more websites offer an option to turn on and off password masking, which is definitely a good thing and the less frustrating option for most You should keep the password masking on when you’re in public places at risk of someone looking over your shoulder; but when you’re in your own home or somewhere private, there’s really no need for it.
Password masking hides characters as bullets or other symbols as you enter a password.
- Your password is only strong if it has several numbers and symbols.
Nearly every time you reset or create a new password, you see very similar requirements; usually something like, “Passwords must be at least eight characters and include one capital letter, one number, and one symbol.” These rules were created to make passwords stronger, but they actually accomplish the opposite—they drive us to choose passwords that we’ve already used somewhere else because it’s easier for us to remember them. But what’s easier for us is easier for hackers too. If they canobtain the password to one of your accounts, they know that you’re probably using that same password somewhere else, and there’s nothing stopping them from trying to use it in as many different places as possible.
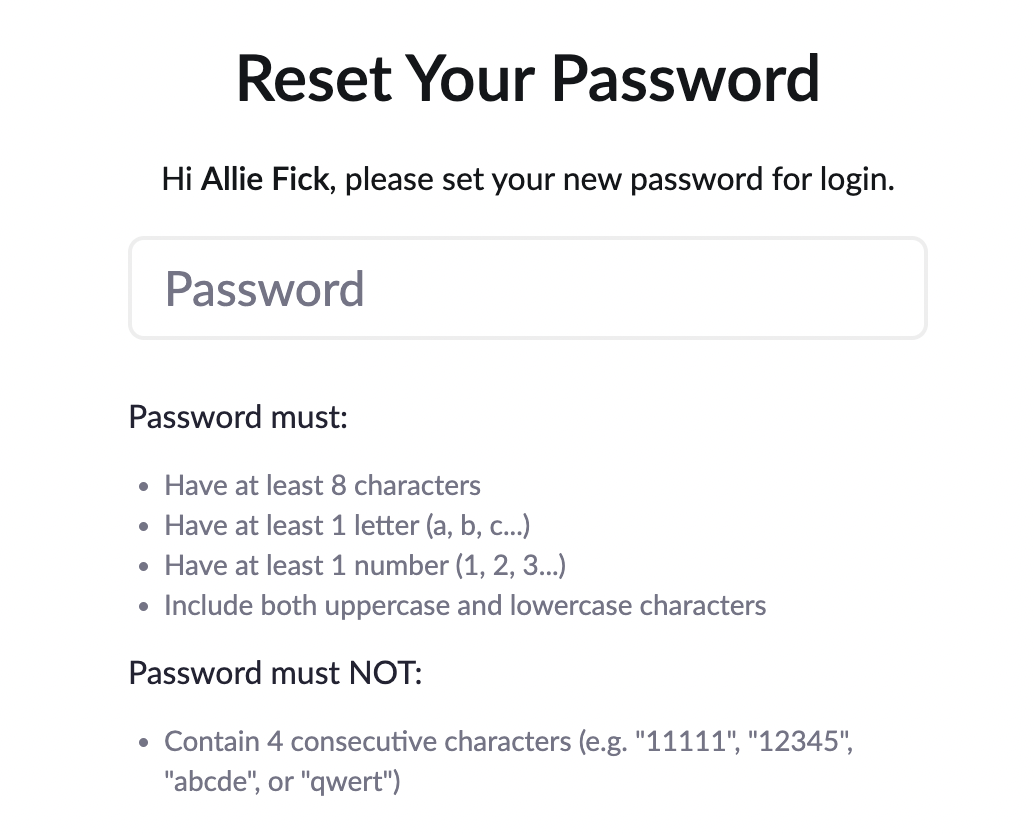
Many websites and applications offer similar guidance to create passwords. This screenshot shows Zoom’s password reset page.
Which rules do we actually need to follow?
So, if it’s okay to write down passwords on Post-Its and see the characters you enter, what can we do to create strong passwords?
The National Institute of Standards and Technology (NIST) digital identity guidelines are a good place to start. They define technical requirements that federal agencies must follow to verify identities and authenticate users. A few key takeaways:
- Use long passwords. Longer passwords are stronger because they’re more difficult to guess.
- Change your password if you think you’ve been involved in a breach.
With these rules in mind, the best strategy to keep your passwords safe is a combination of a few things:
- Use a password manager. Password managers create and remember long, unique passwords for every site you use, so you don’t have to.
- Your password manager is protected by a password. The password you come up with should be used only for your password manager, and it should be a passphrase made up of four or more random words—the more words, the better. If you add in a symbol or a number, that will make it even more secure.
- Use multi-factor authentication everywhere it’s offered. It’s a minor inconvenience and an extra step, but it offers a huge security boost and makes it much harder for hackers to guess your passwords.
When you’re inundated with cybersecurity recommendations, it’s a good idea to occasionally take a step back and evaluate which rules you’re following, and why. Being aware and following the best practices that make the most sense for you in your specific situation will keep you ahead of the bad actors who want to steal your information. To learn more about how to make strong passwords, check out this video.