Time is cloud security’s
#1 adversary
Reduce risks and stop threats fast. Developer and security teams collaborate and accelerate with a unified CNAPP.


















Secure your entire cloud from one place
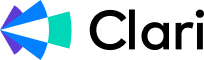
Stop costly mistakes at the source
Empower developers to fix risks before they hit production with software composition analysis (SCA), static application security testing (SAST), infrastructure as code (IaC) security, inline vulnerability scanning, and more.

Don’t waste time on harmless risks
Fix what actually matters. See how attackers can compromise your cloud, then see how these risks connect to running workloads.

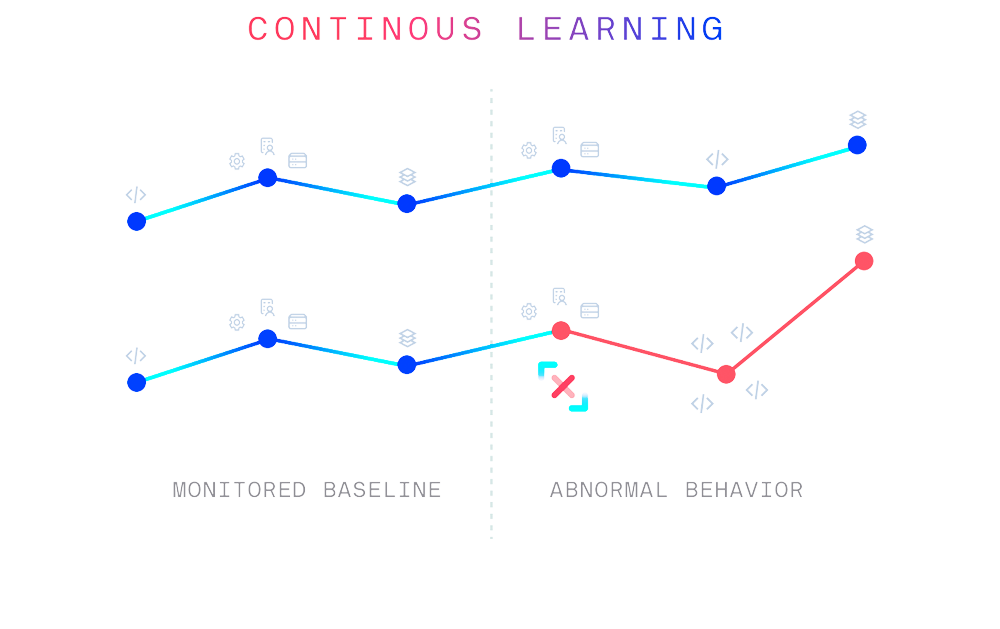
Find known and unknown threats faster
Our patented technology continuously learns your normal to root out suspicious behavior in your cloud activity — including unknown threats like zero-days.
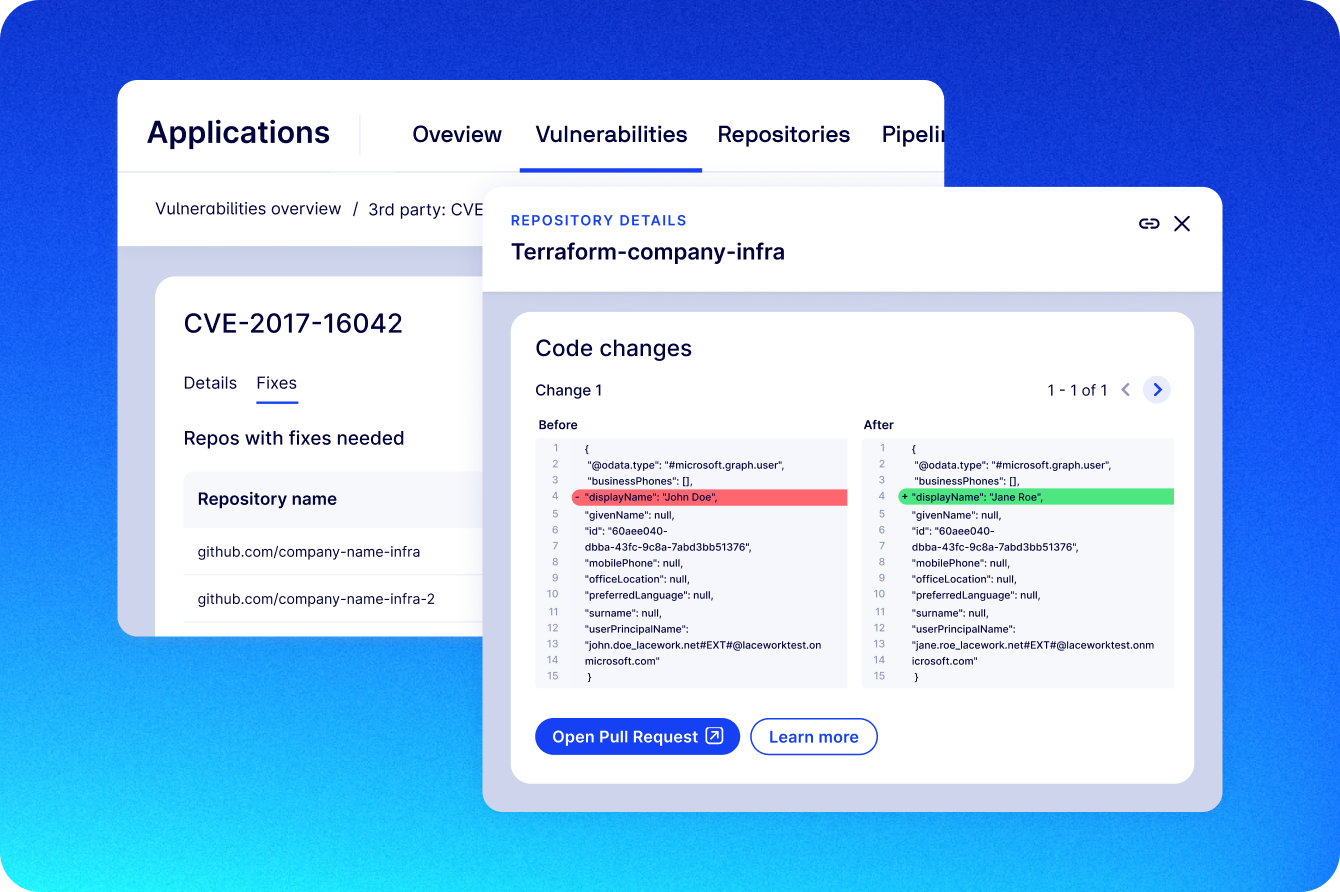
Put audits on autopilot
Automate compliance reporting and evidence gathering with out-of-the-box and custom policies for standards like PCI, HIPAA, NIST, ISO 27001, SOC 2, and more.
Featured Report
Lacework named a Leader in the KuppingerCole Leadership Compass for CNAPP
Read this new report to discover what sets top-tier CNAPPs apart from the rest and which companies are leading the market
Access report
Faster outcomes, better security
81%
See value in less than 1 week
2 - 5
Average tools replaced
100:1
Reduction in alerts
Correlate data from across your cloud


No more siloed data. Our CNAPP automatically connects the dots across build time and runtime to provide unrivaled risk context.
Our CNAPP visualizes your cloud’s relationships, baselines normal behavior, and flags concerning changes — no configuration required.
With Lacework, operationalizing security is a breeze. Flexible deployment options and pre-built integrations get you up and running fast.
“We want to make sure that everything in our cloud environments is visible, and that we can audit it. Lacework has helped with both visibility and auditing, which has really allowed us to grow and mature, and enabled our teams to generate value.”
Steve Lukose
Director of Security Engineering
Read case study
“Lacework helped us deal with this firehose of information that we were getting out of our cloud environments, almost out of the gate. We were able to go from a couple of hundred alerts a day down to just a handful. I’m talking less than 5 — so to go from 200 to 5 is a massive jump.”
John Turner
Senior Security Architect
View case study
“Lacework will enable me to build and operationalize a world class security organization. We value the partnership, and Lacework is the nucleus of our program.”
Paul Groisman
Director of Security
Resources & insights
Featured Insights
Watch Lacework in action
On-demand feature and platform demos and guided tours.




